Resolv USR Stablecoin Exploit: 80 Million Unbacked Tokens Minted, Depeg Triggers Over $25M Loss
Background of Resolv and USR Stablecoin Design
The current DeFi stablecoin landscape can be divided into three main categories: fiat-backed reserves such as USDC, over-collateralized models like MakerDAO, and the more recent emergence of "structured stablecoins." Resolv's USR falls into this third category, aiming to improve capital efficiency while maintaining price stability.
USR's design is not based on a single collateral model. Instead, it integrates hedging strategies with risk tranching mechanisms. For instance, the protocol typically maintains net asset value stability by hedging ETH or other volatile assets and establishes "risk pool" structures, where specific participants absorb losses first during extreme events. Theoretically, this approach increases capital utilization, but it also means the system is no longer a completely self-contained on-chain loop—it now depends on the coordinated operation of multiple components.
This combination of "multi-layered structure and external dependencies" makes the system more efficient under normal market conditions, but it also increases exposure to systemic risks during abnormal situations.
Complete Attack Review: From Minting to Cash Out
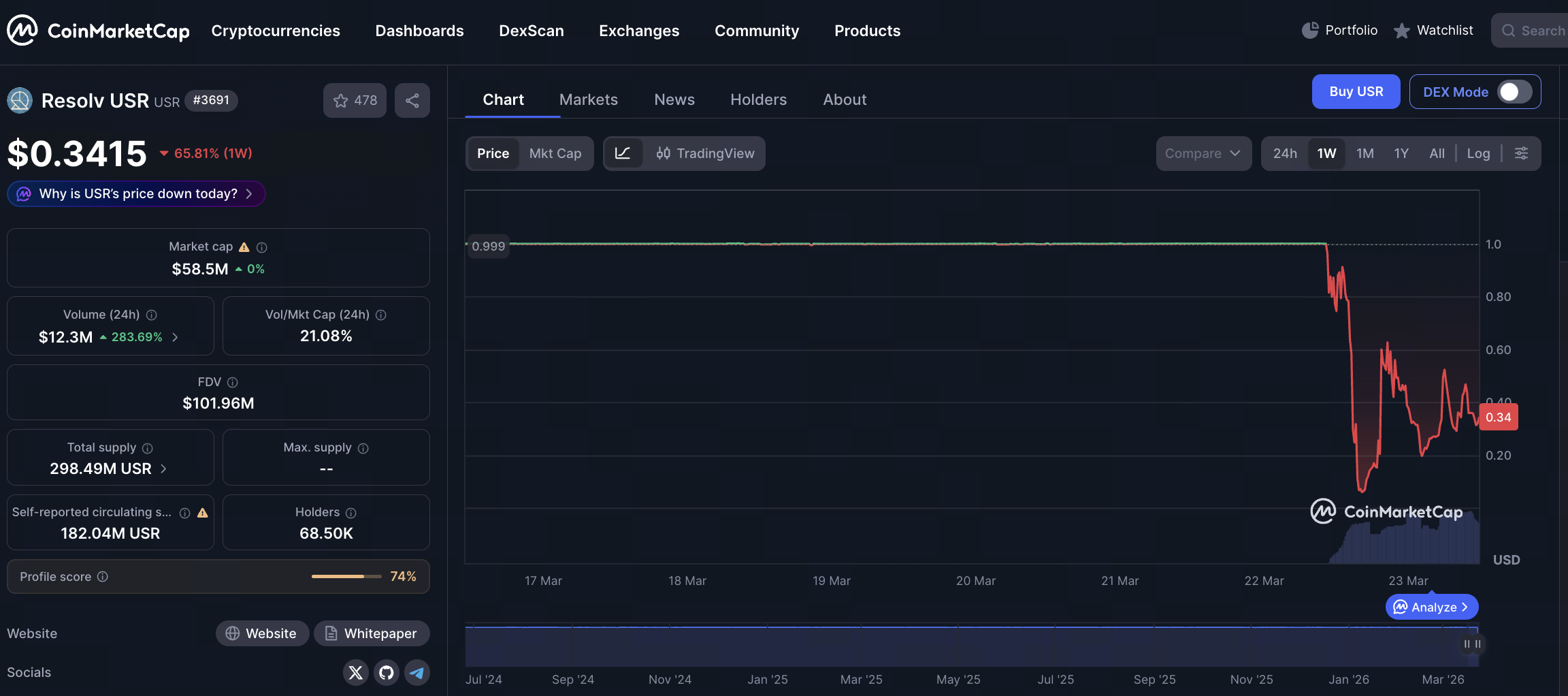
On-chain activity reveals that the Resolv attack was highly structured, following a classic pattern: "uncollateralized minting → liquidity extraction → value transfer."
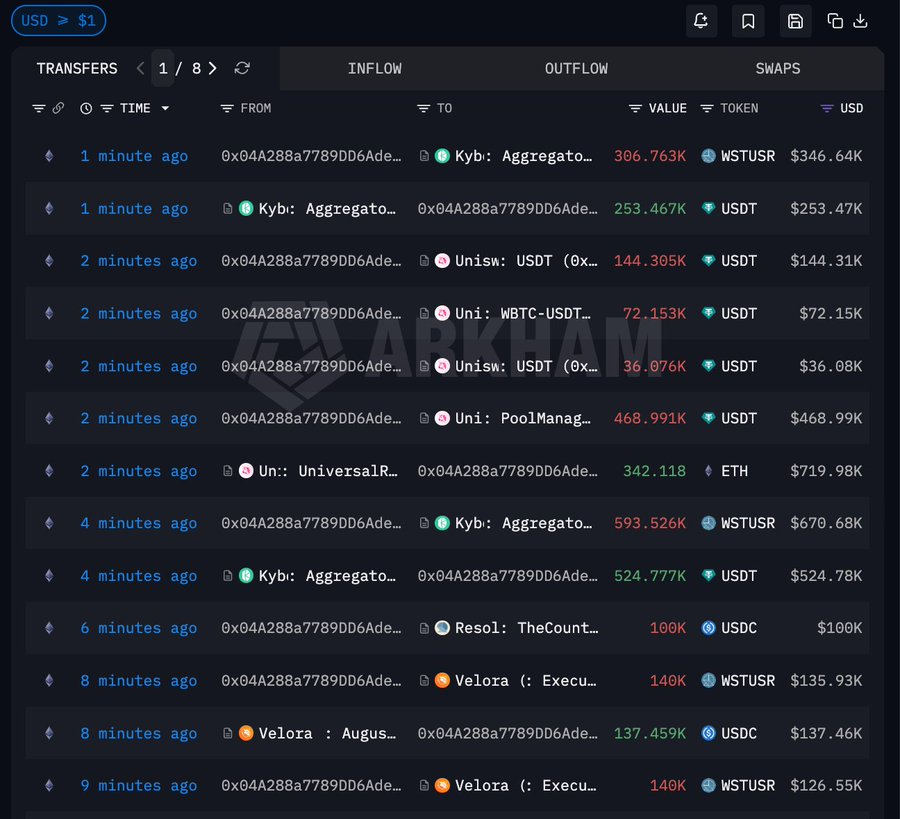 Source: Arkham
Source: Arkham
The attacker entered the system with approximately 100,000 USDC as seed capital, bypassed critical verification mechanisms, and directly minted about 50 million USR. This was the core of the attack, as the system erroneously allowed large-scale stablecoin issuance without sufficient collateral, artificially creating massive "unsupported liquidity."
After the initial minting, the attacker did not immediately liquidate all assets. Instead, about 35 million USR were converted into wstUSR. This step changed the asset format, making it easier to enter various liquidity scenarios or circumvent certain restrictions, while also improving the efficiency of subsequent redemptions.
Next, the attacker systematically exchanged wstUSR for USDC and USDT, gradually withdrawing real assets from stablecoin liquidity pools. During this phase, the automated market maker (AMM) passively absorbed the sell pressure, depleting quality assets in the pool and causing the USR price to fall sharply—a textbook liquidity run.
After converting stablecoins to cash, the attacker further swapped some USDT for ETH, accumulating about $4.55 million in ETH. This move transferred assets into more liquid and less easily frozen mainstream tokens, effectively preserving value and isolating risk.
Core Vulnerability Analysis: Breakdown of the System Trust Mechanism
This incident differs from typical DeFi exploits that target smart contract code vulnerabilities. Instead, it more closely resembles a breach of the system’s trust entry point.
Many modern DeFi protocols rely on more than just on-chain logic for critical operations such as minting, liquidation, or parameter adjustments. They introduce additional verification layers—signature authorization, backend services, or oracle data. These components form an "extended trust model." If any link is compromised, even strictly enforced on-chain logic can produce erroneous results.
Based on the nature of this attack, it is reasonable to infer that the problem likely stemmed from one of the following: a bypass of signature or permission controls, a failure of verification logic under certain conditions, or manipulation of off-chain data sources. Regardless of the specifics, the common flaw was that the system mistakenly recognized an "uncollateralized state" as a "legitimate state."
This type of vulnerability is particularly dangerous because it is not easily detected through code audits. Instead, it depends on the rigor of the overall system architecture.
The Depegging Process: How Liquidity Was Rapidly Drained

In stablecoin systems, maintaining a peg depends not just on theoretical mechanisms but on actual market structure. When a large influx of worthless assets enters the system, liquidity—not protocol logic—is typically the first to collapse.
The USR depegging process followed this pattern. When 80 million uncollateralized tokens entered the liquidity pool, the market quickly became imbalanced: arbitrageurs and attackers continuously sold USR while USDC and USDT were steadily withdrawn from the pool. Since AMMs use asset-ratio-based pricing, one-sided selling rapidly pushed the USR price down.
Several classic phenomena emerged: the price dropped from near $1 to extremely low levels in a short time, quality assets in the pool were quickly depleted, and trading slippage widened significantly. Together, these factors rendered any potential arbitrage correction mechanisms ineffective, ultimately causing the price to freefall.
As a result, the so-called "stable peg" failed, because the key condition for maintaining the peg—ample and healthy liquidity—had already been destroyed.
Loss Structure: How Risk Propagated Through the System
A key feature of this event is that losses were not concentrated on a single party but spread layer by layer through the DeFi structure. Liquidity providers were hit first, as their USDC and USDT were withdrawn from pools in exchange for rapidly depreciating USR. Stablecoin holders also suffered direct price declines, reducing their portfolio values.
At the same time, users in lending markets were affected. When USR was used as collateral or as part of a trading pair, price volatility triggered liquidation mechanisms, forcing some users to close positions. In some architectures, risk pools or insurance mechanisms are designed to absorb shocks, but under extreme stress, these structures often cannot fully cover the losses.
Overall, this risk transmission displayed a clear "chain reaction": a failure in one link quickly escalated into a systemic issue.
Rethinking Stablecoin Mechanisms: Balancing Efficiency and Security
The Resolv USR incident highlights a longstanding dilemma: the trade-off between efficiency and security in stablecoin design. To boost capital efficiency, more projects are lowering collateral ratios, introducing hedging strategies, or adopting complex structures. However, these optimizations increase system complexity.
Greater complexity creates more potential attack surfaces, including permission management, data sources, and execution paths. Without sufficient redundancy and protection, the system becomes vulnerable to extreme events. Designs that rely heavily on liquidity also make market confidence a critical factor. When confidence falters, price stabilization mechanisms struggle to function independently.
In this context, relying solely on "advanced models" cannot resolve these issues and may introduce new risks if not thoroughly validated.
Conclusion: DeFi Stablecoins Enter a High-Complexity Risk Phase
In summary, the USR attack is not an isolated incident but a significant marker in the evolution of DeFi stablecoins. The industry is moving from "simple model risk" to "complex system risk," with attack vectors shifting from individual contract vulnerabilities to multi-layered structural breaches. Attackers exploited the system trust mechanism to mint uncollateralized tokens and extract value through liquidity markets. This process caused both direct economic losses and a clear blow to market confidence.
For future stablecoin design, this incident is a clear warning: in the pursuit of efficiency and innovation, it is essential to reassess system boundaries and trust assumptions. Only by building robust security redundancies and isolation mechanisms at the architectural level can true stability be maintained in complex environments.
Related Articles

In-depth Explanation of Yala: Building a Modular DeFi Yield Aggregator with $YU Stablecoin as a Medium

What is Stablecoin?

Stripe’s $1.1 Billion Acquisition of Bridge.xyz: The Strategic Reasoning Behind the Industry’s Biggest Deal.

False Chrome Extension Stealing Analysis
Top 15 Stablecoins


