Vitalik’s Hong Kong Speech Explained: Why Ethereum’s Next 5-Year Roadmap Bets on zkVM, Account Abstraction, and Post-Quantum Security
1. Key Takeaway: Redefining Ethereum’s Role
Vitalik’s remarks in Hong Kong can be distilled into a single idea: Ethereum’s essence isn’t about being the “fastest execution layer,” but rather serving as a “public bulletin board and shared computation layer.”
While this definition may sound abstract, it fundamentally shifts the framework for discussion. Previously, the market often compared public blockchains using metrics like TPS and transaction confirmation speed, but Vitalik highlights a different value proposition:
-
Public Bulletin Board: Any application can post transactions, hashes, encrypted data, and more to a globally visible, sequentially verifiable public layer.
-
Shared Computation Layer: Digital objects are maintained collectively by code rules, enabling assets, identities, organizational governance, and collaboration to operate on a unified foundation of trust.
With these two capabilities combined, Ethereum’s scope extends beyond DeFi to encompass broader “high-value collaborative systems.” Examples include:
-
Financial scenarios demanding strong, verifiable records;
-
Prediction markets requiring integration between on-chain assets and off-chain information;
-
Governance and voting systems that need both privacy and auditability.
Ultimately, the core message is this: Ethereum’s ambition is to become a long-term, trustworthy base layer for societal settlement and collaboration—not simply to win a short-term performance contest.
2. Roadmap Focus: Scaling, Security, and Verifiability Advancing Together
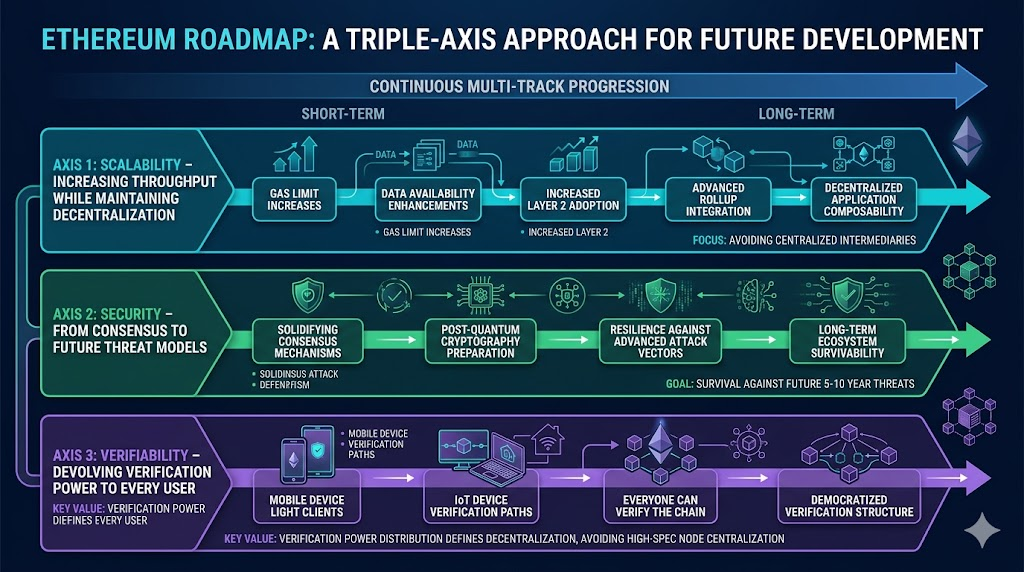
From a structural perspective, Vitalik isn’t advocating for a “scale first, then secure” approach. Instead, he’s pushing for three priorities in parallel.
2.1 Scaling: Raising the Ceiling Without Compromising Decentralization
In the near term, scaling improvements will continue—including raising the gas limit and enhancing data availability. The goal isn’t simply to “make the chain bigger,” but to enable more applications to compose without relying on centralized intermediaries.
2.2 Security: Expanding from Consensus Security to Future Threat Models
Vitalik repeatedly referenced post-quantum preparedness, signaling a shift in threat modeling from “current attack surfaces” to “potential attack vectors over the next 5–10 years.” Security objectives are evolving from merely “avoiding breaches today” to ensuring “long-term survivability.”
2.3 Verifiability: Empowering All Devices to Verify
Vitalik stressed that “everyone should be able to verify the chain”—including mobile and IoT devices.
This underscores a critical value: decentralization is not just about node count, but about the distribution of verification power. If only a few high-spec nodes can verify, the system’s political and economic structure inevitably centralizes.
3. Five Key Technical Pillars: zkVM, AA, Privacy, Post-Quantum, Data Expansion
Vitalik’s address spotlighted five technical directions to watch.
3.1 zkVM: Making “Provability” Standard
The strategic value of zkVM isn’t a one-off performance leap, but the ability to verify chain execution results more efficiently. If this approach matures, we’ll see:
-
Lightweight devices gaining verification capabilities, reducing user reliance on third-party nodes;
-
Scaling and decentralization no longer being mutually exclusive.
3.2 Account Abstraction (AA): Reinventing Wallet Experience and Security
Account abstraction introduces greater transaction flexibility by decoupling verification logic from execution logic, directly impacting:
-
The adoption of smart contract wallets;
-
Productization of features like gas sponsorship, recovery mechanisms, and multi-signature strategies;
-
Easier integration of post-quantum signatures and privacy strategies at the wallet level.
This means wallets will evolve from simple private key containers to programmable, secure entry points for users.
3.3 Privacy Enhancements: On-Chain Transparency and User Privacy Can Coexist
Vitalik made it clear: many applications inherently require “on-chain publishing and off-chain interpretation.”
This is why privacy isn’t just a secondary feature—it’s a prerequisite for mainstream public blockchain adoption.
Future directions may include:
-
Ensuring commitments and verifiable order on-chain;
-
Protecting sensitive information off-chain through cryptographic protocols;
-
Offering provable, minimally exposed interactions where necessary.
3.4 Post-Quantum Signatures: Prepare Now, Transition Later
Vitalik noted that post-quantum signature schemes have been researched for years, with efficiency and cost as the main challenges.
This marks a shift from “is there a solution” to “can it be deployed at scale.”
In the medium to long term, the key isn’t just the algorithm, but the migration path—how to transition the current account system smoothly, avoiding abrupt changes.
3.5 Data Expansion: Raising the Ceiling for On-Chain and Off-Chain Applications
Defining Ethereum as a public data publishing layer makes data expansion a core infrastructure priority, not just an optimization. This will directly impact L2 cost structures, composability, and cross-protocol efficiency.
4. Real Demands on L2 and Application Layers: Not Just “A Faster Chain”
Vitalik’s view on L2 deserves industry-wide reflection. The main takeaway: a meaningful L2 isn’t just a faster copy of an existing chain, but a system where off-chain components and on-chain security boundaries are clearly coordinated.
This raises expectations for project teams:
-
Identify which parts must be on-chain and which can be off-chain;
-
Explain how off-chain modules are constrained and verified;
-
Prove that users can exit, verify, and self-custody even under worst-case scenarios.
If the focus is solely on “cheaper and faster” without credible exit or verification paths, performance gains simply translate into structural credit risk.
5. Actionable Insights for Developers, Startups, and Investors
Vitalik’s speech provides actionable guidance for every stakeholder.
5.1 For Developers
-
Prioritize learning AA and zk engineering stacks—not just front-end interaction layers.
-
Design applications with verifiability and failure exit paths as defaults.
-
Treat privacy and permission control as architectural concerns, not afterthoughts.
5.2 For Startups
-
Shift product strategy from “feature stacking” to “trusted collaborative efficiency.”
-
Choose architectures with clear on-chain/off-chain separation, avoiding heavy, centralized operations.
-
In fundraising narratives, focus less on TPS and more on security and compliance resilience.
5.3 For Investors and Researchers
Going forward, the focus should be on who consistently delivers verifiability, security, and user sovereignty—not just scaling narratives.
-
When evaluating projects, ask:
-
Can users self-verify key states?
-
Is safe exit possible in extreme scenarios?
-
Does the protocol have a post-quantum migration plan?
-
6. Risks and Uncertainties: Critical Variables from Vision to Execution
No roadmap guarantees results—especially in complex systems like public blockchains. Key risks highlighted in the speech include:
-
Engineering complexity: zkVM, post-quantum, and privacy protocols demand rigorous implementation and auditing.
-
Ecosystem coordination: Clients, wallets, applications, L2s, and infrastructure require long-term collaboration.
-
User education: Verifiability doesn’t automatically mean usability; user experience remains critical for adoption.
-
Market expectation mismatch: Capital markets prefer short-term metrics, while protocol evolution is a long-term process.
The most robust evaluation framework is:
-
Short-term: milestone delivery;
-
Medium-term: ecosystem adoption rates;
-
Long-term: sustainable operation even if the core team changes.
Conclusion: From a “Performance Race” to a “Trust Race”

Image source: Gate Market Page
The value of Vitalik’s speech is in clarifying Ethereum’s long-term vision: it’s not about being the fastest chain, but about being the most trustworthy public foundational layer.
In an era shaped by AI, quantum computing, and evolving global regulation, the rarest qualities aren’t short-term speed, but:
-
Verifiability;
-
Survivability;
-
Composability;
-
Sustainable evolution.
Viewed through the lens of 2026, this speech sends a clear message: public blockchain competition is shifting from “who’s faster” to “who’s more trustworthy.” That will determine which infrastructure supports the next wave of large-scale applications.
References: Foresightnews
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


