MakinaFi suffers flash loan attack! 1299 ETH stolen, MEV bots split the loot

MakinaFi on January 20th suffered a flash loan attack, losing 1,299 ETH (approximately $4.1 million). The hacker manipulated Curve pools for arbitrage, with an MEV bot front-running and earning 0.13 ETH. The stolen funds are stored in two wallets that have not yet been mixed.
MakinaFi Flash Loan Attack Breakdown
DeFi yield and asset management platform Makina Finance encountered a major security vulnerability. On January 20th, hackers attacked one of its stablecoin pools, stealing about 1,299 ETH, worth approximately $4.1 million at current prices. The attack was initially reported by blockchain security firm PeckShield. Within minutes, on-chain trackers identified the stolen funds, which are stored in two wallets.
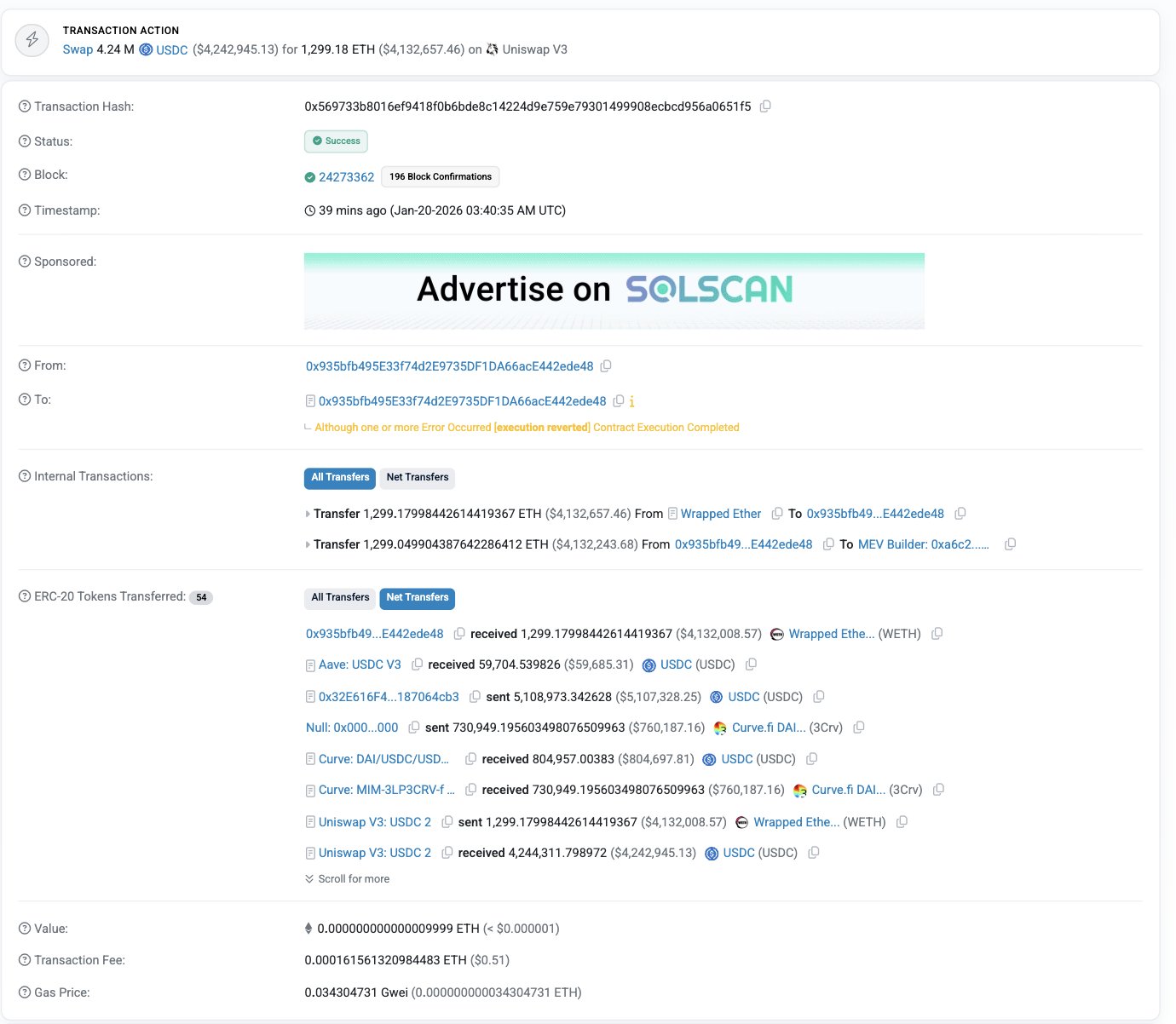
The target of this attack was MakinaFi’s DUSD/USDC Curve liquidity pool. Specifically, the pool is built on Curve Finance, connecting Dialectic’s yield tokens DUSD and USDC. The attack employed a classic flash loan technique. This means the attacker borrowed large amounts of cryptocurrency within seconds, manipulated the prices using these funds, and drained the pool and repaid the loan in a single transaction.
MakinaFi Flash Loan Attack Steps
Step 1: Borrow large amounts of USDC and ETH from Aave and Morpho
Step 2: Conduct a series of token swaps on Curve and Uniswap to manipulate prices
Step 3: Exploit price imbalances to extract tokens worth far more than they should
Step 4: Repay the flash loan and profit 1,299 ETH
The event summary is as follows: the attacker borrowed funds from protocols like Aave and Morpho, then performed a series of token swaps on Curve and Uniswap. By manipulating the prices within the pools, they successfully extracted tokens worth far more than their actual value. Ultimately, they stole 1,299 ETH. The entire attack was completed within a single block, which is a typical characteristic of flash loan attacks.
The principle of flash loans is based on the atomicity of DeFi transactions. On Ethereum, a transaction can include multiple steps that either all succeed or all fail. The attacker uses this feature to borrow, attack, arbitrage, and repay all within one transaction, without any collateral. If any step fails, the entire transaction reverts, and the attacker loses nothing (only gas fees). This zero-risk attack mode makes flash loans a preferred tool for DeFi hackers.
MEV Bots and Hackers Competing for Profits
It’s not just hackers making money. An MEV (Maximal Extractable Value) bot also participated. MEV bots scan the blockchain for profitable transactions and try to front-run them. In this case, an MEV address starting with 0xa6c2 inserted itself into the transaction bundle and earned a small profit. It only made about 0.13 ETH. But this illustrates how congested and competitive Ethereum transactions have become.
MEV is a unique phenomenon on blockchains. Miners or validators can reorder, insert, or censor transactions within blocks to extract additional profits. MEV bots specifically look for opportunities, such as front-running large trades or executing arbitrage ahead of others.
In the MakinaFi attack, the MEV bot detected the hacker’s malicious transaction and judged it profitable. It paid higher gas fees to insert its own transaction ahead of the hacker’s attack, thus sharing in the profit. The phenomenon of “hackers being front-run by MEV” is darkly humorous but also reveals the complexity and fierce competition within the Ethereum ecosystem. Even hackers now have to compete with bots for profits. The crypto world is truly a wild frontier.
PeckShield’s report specifically states: “The hacker exploited MEV Builder (0xa6c2…) to front-run the attack.” This statement is quite ironic—usually, MEV bots front-run user transactions, but in this case, the MEV bot front-ran the hacker’s attack transaction. This layered front-running (MEV front-running the hacker’s attack) demonstrates the complex game of on-chain transaction competition.
Stolen Funds Flow and Tracking Challenges
The stolen ETH is currently stored in two wallets: 0xbed2…dE25 holding about $3.3 million, and 0x573d…910e holding about $880,000. So far, these funds have not been mixed or transferred through privacy tools. This gives investigators a chance to track each transaction.
Security firms including PeckShield, ExVul, and TenArmor have warned users to revoke contract permissions and avoid interacting with MakinaFi contracts for now. Revoking permissions means canceling prior authorizations that allow MakinaFi’s smart contracts to access your wallet. In DeFi, when you interact with a protocol, you often need to approve it to operate your tokens. If the protocol is compromised or has vulnerabilities, these permissions can be maliciously exploited.
Makina has not issued an official statement yet. This silence may be because the team is assessing the damage and formulating a response, but for affected users, lack of timely communication can increase panic and distrust. In DeFi security incidents, quick and transparent communication is crucial. The team should immediately confirm the event, clarify the scope, provide user protection measures, and publish investigation updates.
The fact that funds have not yet been mixed is a positive sign. Hackers often quickly transfer stolen funds to privacy protocols (like Tornado Cash) or bridge them to other chains to break traceability. Currently, the funds remain in the original wallets, which may indicate the hackers are waiting for the right moment (e.g., when attention subsides) or seeking optimal money laundering routes. This window offers opportunities for law enforcement and white-hat hackers to intervene.
Hard Lessons for DeFi Users and Protective Recommendations
On January 20th, according to MakinaFi’s official statement, the platform received reports of a suspected security incident involving the $DUSD Curve pool. The preliminary assessment indicates only the DUSD liquidity position was affected; other assets and deployments have not shown anomalies. As a precaution, the platform has activated safety mode on all Machines and advised DUSD liquidity providers to withdraw funds promptly. The official team is fully investigating the scope of the incident and will announce detailed progress and solutions later.
MakinaFi is known for offering advanced yield strategies based on DeFi tools like Curve, Aave, and Uniswap. Its DUSD token aims to generate yield through on-chain strategies. But this attack reveals a harsh reality: even complex and well-designed DeFi systems still have vulnerabilities. Flash loan attacks remain one of the most common methods for hackers to steal funds.
Stablecoin pools are often prime targets because they hold large liquidity. In early 2025 and 2026, DeFi hacker attacks have already caused billions of dollars in losses to users. The lesson is simple: if your funds are on-chain, they are always at risk. DeFi is rapidly evolving, and hacker tactics are evolving faster. Therefore, even in 2026, this incident has reignited concerns about DeFi platform risks. Moreover, this is not a minor glitch but a clean, swift, and effective attack.
Five Protective Measures for DeFi Users
Regularly revoke permissions: periodically review and revoke permissions for unused protocols
Diversify funds: do not keep all assets in a single protocol
Choose audited protocols: prioritize mature platforms with multiple security audits
Pay attention to security alerts: follow real-time alerts from security firms like PeckShield
Understand risks: recognize that high yields often come with high risks
From a broader perspective, the MakinaFi attack exemplifies the DeFi security crisis of 2026. Despite technological advances and improved security tools, hackers’ methods continue to evolve. Flash loans, reentrancy attacks, price manipulation, governance exploits—these tactics are ever-changing. For DeFi projects, security is not a one-time audit but an ongoing battle and upgrade process. For users, understanding the inherent risks of DeFi and avoiding blind pursuit of high yields are the first steps to protecting assets.
Related Articles
Vitalik's sale plan is 94% complete, with 15,500 ETH sold since February 2.