Cryptography Engineer: Quantum Computers Pose No Threat to “128-bit Symmetric Encryption”

Cryptography engineer Filippo Valsorda published a technical analysis article on April 20, 2026, arguing that even at the most optimistic pace of development, quantum computers cannot crack 128-bit symmetric encryption (AES-128) in the foreseeable future, and pointing out that the industry has misunderstood “post-quantum cryptography.”
Key takeaways from the Valsorda paper: Grover’s algorithm cannot effectively run in parallel
(Source: Filippo Valsorda)
According to Valsorda’s analysis article, a common industry misconception is that the Grover algorithm of quantum computers will “halve” the security strength of a 128-bit symmetric key to 64 bits. This claim overlooks a crucial limitation of Grover’s algorithm: its steps must be executed serially, and forcing parallelization would sharply increase the total computational cost.
Valsorda’s calculations show that the total number of operations required to break AES-128 is about 2¹⁰⁴·⁵ operations; by comparison, using Shor’s algorithm to break 256-bit elliptic-curve cryptography would require about 2²⁶ operations (citing a 2026 study by Babbush et al.). The two differ by about 2⁷⁸·⁵ times. Valsorda notes that this gap makes mounting a Grover attack on AES-128 entirely impractical in practice.
A unified stance from NIST, BSI, and academia
Based on the official documents Valsorda cites, the U.S. National Institute of Standards and Technology (NIST) explicitly states in its post-quantum cryptography FAQ that “Grover’s algorithm may provide almost no advantage in attacking AES; AES-128 will remain secure for the next several decades,” and confirms that “existing applications can continue to use 128-bit AES keys.” NIST IR 8547 also prohibits algorithms vulnerable to quantum attacks in 2035, while confirming that all AES key lengths remain acceptable.
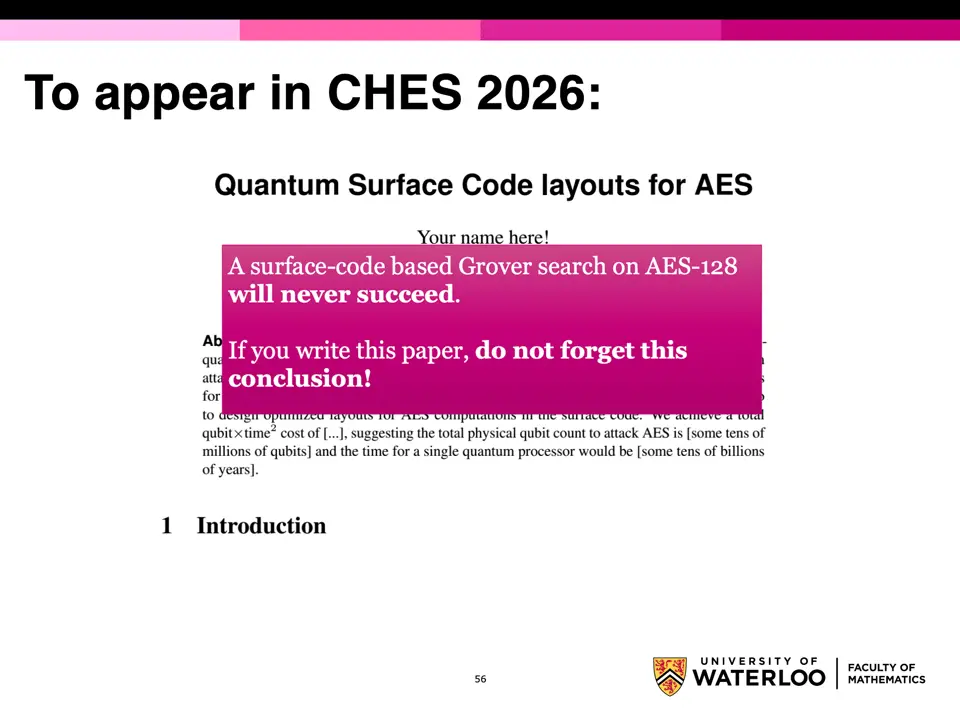
In its report “Cryptographic Mechanisms: Recommendations and Key Lengths,” Germany’s Federal Office for Information Security (BSI) recommends using AES-128, AES-192, and AES-256 in new cryptographic systems. Samuel Jaques, an assistant professor of cryptography at the University of Waterloo, said in a 2024 research presentation: “Grover search based on fault-tolerant surface codes will never succeed on AES-128.”
The real priorities for post-quantum migration
According to Valsorda’s conclusion, the only urgent task for post-quantum encryption migration is to replace asymmetric encryption that is vulnerable to attacks by Shor’s algorithm, including RSA, ECDSA, and ECDH. Valsorda points out that using limited resources to upgrade symmetric keys (128→256 bits) is an unnecessary operation; it would increase system complexity, fragment and distract coordinated resources, and interfere with the truly urgent work of replacing vulnerable asymmetric encryption.
Frequently Asked Questions
Why does Valsorda believe that Grover’s algorithm cannot threaten AES-128?
According to Valsorda’s analysis article, the steps of Grover’s algorithm must be executed serially and cannot be effectively parallelized; after forced parallelization, the total computational cost to break AES-128 is about 2¹⁰⁴·⁵ operations, which is roughly 2⁷⁸·⁵ times higher than the cost of breaking 256-bit elliptic-curve cryptography with Shor’s algorithm.
What is NIST’s official position on whether AES key lengths need to be doubled?
According to the post-quantum cryptography FAQ cited in the Valsorda article, NIST explicitly states that AES key lengths should not be doubled to address quantum threats, confirming that AES keys of 128 bits, 192 bits, and 256 bits are all still secure in the post-quantum era.
What is the true urgent task of post-quantum cryptography migration?
Based on Valsorda’s conclusion, the only urgent task is to replace asymmetric encryption algorithms that are vulnerable to attacks by Shor’s algorithm (such as RSA, ECDSA, ECDH, etc.), rather than upgrading symmetric key lengths; upgrading symmetric keys is an unnecessary operation that increases complexity and diverts resources.