Spring Festival Asset Security Guide: How to Protect Your Tokens While Visiting Family and Friends and Relaxing?
Article by: imToken
As the Lunar New Year approaches, it’s a time for bidding farewell to the old and welcoming the new, and also a moment to reflect once again:
In the past year, have you fallen into any Rug Pull projects that ran away? Have you bought in because of hype from KOLs and ended up stuck? Or suffered from increasingly rampant phishing attacks, losing assets due to clicking malicious links or signing contracts by mistake?
Objectively, the Spring Festival itself doesn’t create risks, but it can amplify them—when capital flows increase, attention is divided by holiday activities, and trading speeds up, any small mistake can be magnified into a loss.
Therefore, if you’re planning to adjust your positions or organize funds before the holiday, it’s a good idea to give your wallet a “pre-holiday safety check.” This article will explore several real and high-frequency risk scenarios, systematically outlining specific actions that ordinary users can take.
1. Beware of AI Face Swap and Voice Simulation Scams
Recently, the trending SeeDance 2.0 has once again made everyone realize that in an era where AGI is rapidly advancing, “seeing is believing” and “hearing is trusting” are becoming invalid.
Starting from 2025, AI-based video and voice scams have become significantly more sophisticated, including voice cloning, face swapping in videos, real-time expression imitation, and tone simulation—all entering a low-threshold, scalable “industrialized” phase.
In fact, AI now can accurately reproduce a person’s voice, speech pace, pauses, and even micro-expressions. This means that during the Spring Festival, such risks are especially likely to be amplified.
For example, on your way home or during a family gathering, your phone might pop up a message from a “friend” via Telegram or WeChat, with urgent tone, claiming their account is restricted, requesting a quick transfer of a small amount of tokens for account recovery,红包周转, or temporary advance.
The voice sounds natural, and the video even shows a “real person,” so how do you judge when your attention is divided by holiday distractions?
In previous years, video identity verification was almost the most reliable method, but today, even if the other person is on camera talking to you, it’s no longer 100% trustworthy.
In this context, simply watching a video or listening to a voice clip is no longer sufficient for verification. A more reliable approach is to establish an independent verification mechanism outside online communication with core circles (family, partners, long-term collaborators), such as a shared offline secret code or details that cannot be inferred from public information.
Additionally, it’s important to re-examine a common risk pathway: links forwarded by acquaintances. During the Spring Festival, “on-chain red envelopes” and “airdrops” are highly susceptible to viral spread within the Web3 community. Many people aren’t tricked by strangers but trust friends’ forwarding, clicking on carefully disguised authorization pages.
Therefore, everyone should remember a simple yet crucial principle: Never click on unknown links directly from social platforms, and never authorize transactions— even if they come from “friends.”
All on-chain operations should be done through official channels, bookmarked URLs, or trusted portals, rather than within chat windows.
2. Conduct a “Year-End Wallet Cleanup”
If the first risk stems from trust being faked by technology, the second comes from long-term hidden exposure accumulated in our own wallets.
It’s well known that authorization is the most fundamental and often overlooked mechanism in DeFi. When you operate within a DApp, you’re essentially granting the contract token control—this could be a one-time permission or an unlimited allowance, valid for a short period or still active long after you’ve forgotten about it.
Ultimately, this isn’t necessarily an immediate risk, but it’s a persistent exposure. Many users mistakenly believe that as long as assets aren’t stored directly in the contract, there’s no security issue. However, during bull markets, users often try various new protocols, participate in airdrops, staking, mining, and on-chain interactions, accumulating authorization records. When hype subsides, many protocols are no longer used, but permissions remain.
Over time, these residual authorizations become like a bunch of keys left uncollected. If a vulnerability occurs in a protocol you’ve long forgotten, it can lead to losses.
Spring Festival is a natural opportunity for organization. Using the relatively calm pre-holiday period to systematically review your authorization records is highly recommended:
- Revoke permissions you no longer use, especially unlimited allowances;
- Use limited permissions for large assets instead of granting full, long-term access;
- Separate management of long-term stored assets and daily operational assets, creating a layered structure of hot and cold wallets.
In the past, many users relied on external tools (like revoke.cash) for such checks. Now, mainstream Web3 wallets like imToken have built-in authorization inspection and revocation features, allowing you to view and manage your permissions directly within the wallet.
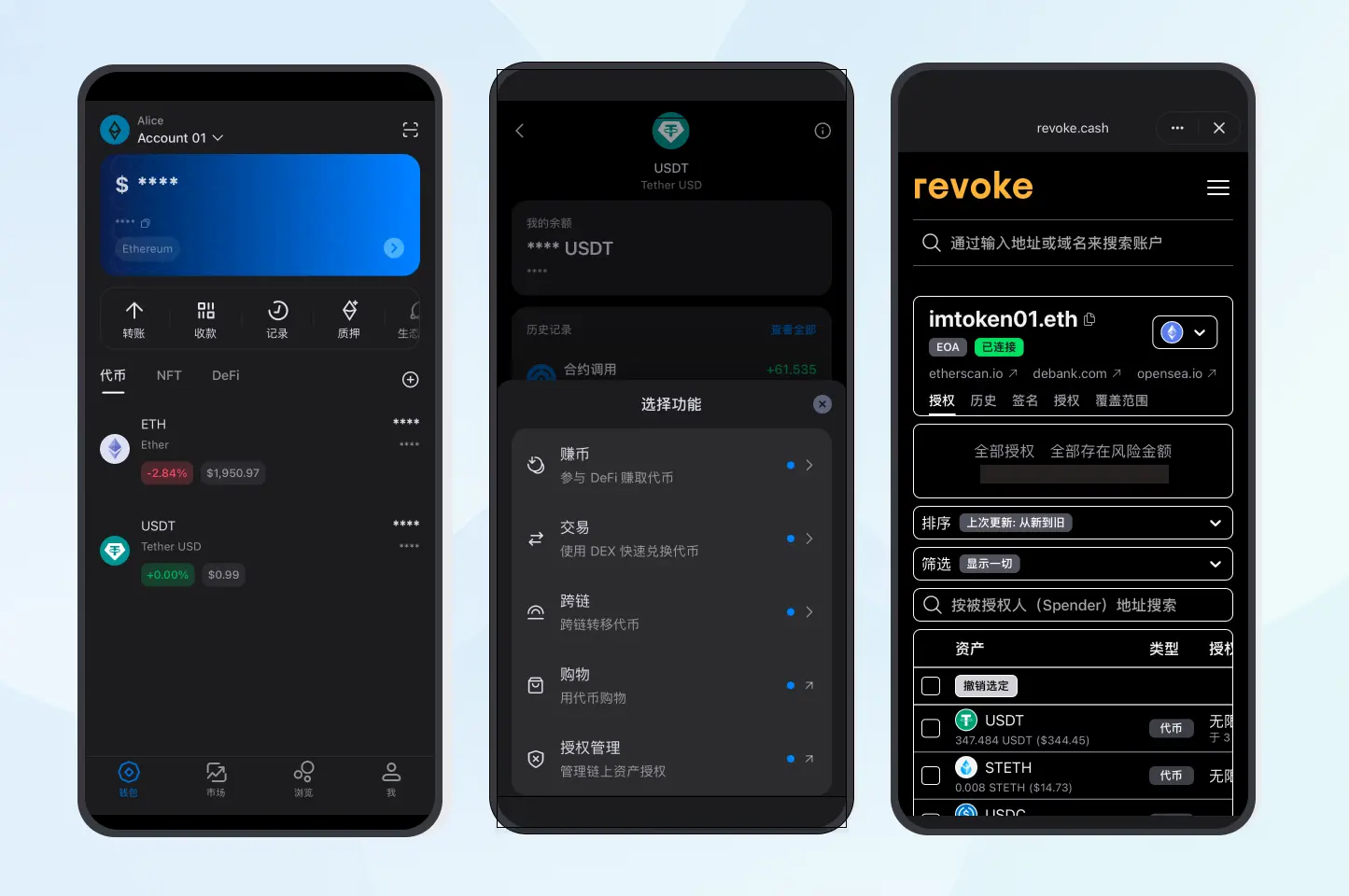
Ultimately, wallet security isn’t about never granting permissions but following the principle of least privilege—only granting what’s necessary at the moment and retracting permissions when no longer needed.
3. Don’t slack on travel, socializing, and daily operations
If the first two risks stem from technological fakeouts and accumulated permissions, the third arises from environmental changes.
Travel during the Spring Festival (going home, traveling, visiting friends and relatives) often involves frequent device switching, complex network environments, and dense social interactions. In such settings, the vulnerabilities in private key management and daily operations are greatly amplified.
A typical example is mnemonic management. Saving a screenshot of your seed phrase in your phone album, cloud storage, or forwarding it via instant messaging for convenience is common, but in mobile scenarios, this convenience is also the biggest hidden danger.
Remember, mnemonics must be kept physically isolated, avoiding any online storage. The bottom line for private key security is to be completely offline.
Social scenarios also require boundary awareness. Showing large asset balances or discussing specific holdings at gatherings can unintentionally create risks. Be especially cautious of behaviors that, under the guise of “sharing experience” or “teaching,” lead others to download fake wallet apps or plugins.
All wallet downloads and updates should be done through official channels, not via links in chat windows.
Before making a transfer, always verify three things: network, address, and amount. There have been many cases where whales mistakenly sent assets to addresses with similar starting or ending characters, resulting in huge losses. Phishing attacks using similar address patterns have become industrialized in recent months:
Hackers generate large pools of addresses with similar start or end characters. When a transfer occurs to one of these addresses, they quickly find matching addresses in their seed database and execute related transfers, waiting for victims to make mistakes.
Some users copy addresses directly from transaction records, only checking the first and last few characters, which is risky. According to Yuán Cén, founder of SlowMist, phishing attacks targeting start/end characters are “net casting attacks—volunteers get caught in the net, it’s a game of probability.”
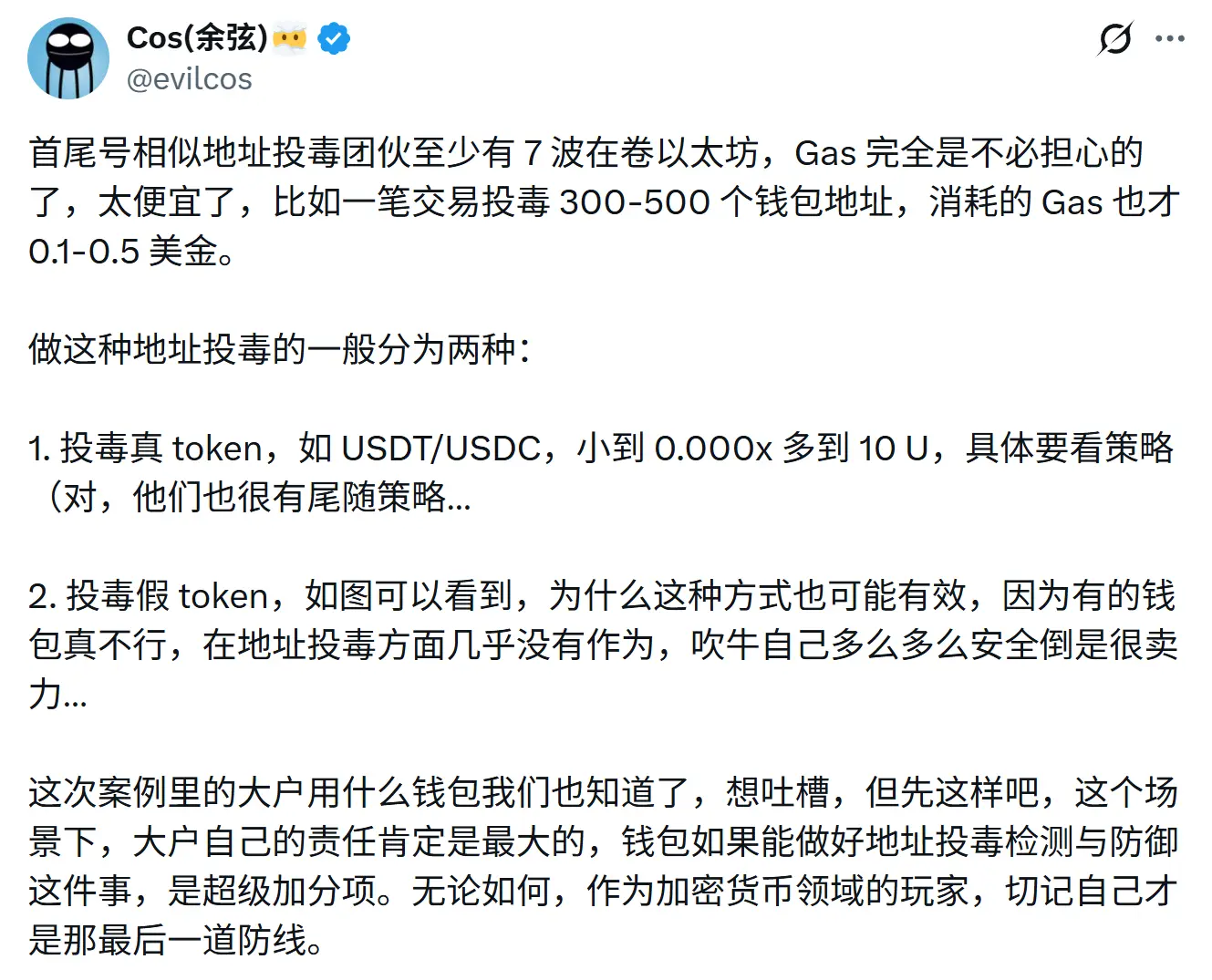
Because gas costs are low, attackers can batch poison hundreds or thousands of addresses, waiting for a few users to slip up during copying and pasting. Once successful, the profit far exceeds the cost.
The core issue isn’t technical complexity but daily habits:
- Fully verify address characters, not just start/end;
- Don’t copy addresses from history without checking;
- Test new addresses with small transactions first;
- Use address whitelist features to manage frequently used addresses.
In the current decentralized ecosystem dominated by EOA accounts, users are always their own first line of defense and last safeguard (see also “$3.35 billion ‘Account Tax’: When EOAs Become Systemic Costs, What Can AA Bring to Web3?”).
Final Words
Many people feel that on-chain security is too risky and not user-friendly.
Honestly, Web3 can’t guarantee a zero-risk environment, but it can be a risk-manageable one.
For example, the Spring Festival is a slowdown period and an ideal window for restructuring risk. Instead of rushing to operate during the holiday, it’s better to complete safety checks in advance; instead of fixing problems afterward, optimize permissions and habits beforehand.
Wishing everyone a safe and smooth Spring Festival, and may your on-chain assets remain stable and worry-free in the new year.